HR teams in 2026 handle more sensitive data than ever before. From Social Security numbers to health records to performance reviews, the volume and variety of employee information continues to grow. Meanwhile, data protection laws span multiple jurisdictions simultaneously, creating complex compliance obligations for any organization with distributed teams.
Here is the core challenge. Employers must collect enough data to manage payroll, benefits, and performance effectively. Yet collecting too much creates unnecessary risk. Research shows that 31% of HR managers acknowledge they need better employee data protection solutions. This signals a widespread pain point across industries and company sizes.
The reputational damage from a data breach extends far beyond regulatory fines. It directly erodes employee trust and can trigger serious talent retention issues. Companies hiring across multiple regions now face overlapping regulatory obligations that demand a coordinated approach to protecting personal data throughout the employee lifecycle.
What Is HR Data Protection In The Employee Lifecycle
HR data protection combines technical safeguards, organizational policies, and legal compliance mechanisms that keep employee personal information confidential, accurate, and accessible only to authorized personnel. This responsibility spans the entire employee lifecycle from the first CV received through offboarding and retention periods that may last years.
The data involved includes names, addresses, banking information, medical records, performance reviews, disability status, and citizenship documentation. This information attracts three primary risks: unauthorized access leading to identity theft, regulatory penalties under laws like the General Data Protection Regulation, and lasting reputational damage. Effective data protection measures address all three concerns through a combination of technical controls and clear policies, as outlined in our broader guide to employee data protection in HR systems.
Legal Foundations Of HR Data Protection Worldwide
Most organizations with geographic spread face simultaneous compliance obligations. A US company with European employees must meet GDPR requirements. A global firm navigating Brazil’s LGPD, China’s personal information protection law, and Singapore’s personal data protection act creates exponentially higher complexity than single jurisdiction compliance.
GDPR and UK GDPR set the regulatory bar with fines reaching 4% of global annual turnover or €20 million. Key obligations include establishing a lawful basis for processing data, maintaining transparency about data collection and use, respecting retention limits, and honoring data subject rights, including access and deletion requests within 30 days.
The California Consumer Privacy Act and its successor, CPRA, grant California employees rights to know what personal information is collected, delete data, and correct inaccuracies. The Fair Credit Reporting Act applies when HR conducts background checks or credit reporting activities. The Health Insurance Portability and Accountability Act governs health plan data with potential fines up to $50,000 per incident.
Emerging regimes add further complexity. Brazil’s LGPD follows GDPR closely. China’s PIPL requires explicit consent for cross-border data transfers. India’s Digital Personal Data Protection Act 2023 is now being implemented. Employment contracts, works council agreements, and union rules also shape how HR can process employee data in many jurisdictions.
Key Employee Data Collection Points
Employee data enters HR systems through multiple touchpoints across the lifecycle. Each stage introduces unique risks, making it essential to identify, track, and secure every data collection point with clear controls, supported by structured employee lifecycle management practices.
Recruitment Data Collection Sources
During the hiring process, HR typically collects CVs, cover letters, contact details, work history, and assessment results. Recruiters often store these documents in personal email or messaging apps rather than secure centralized systems. This creates significant exposure. Best practice involves centralizing recruitment data into secure applicant tracking systems with proper access controls and audit logging.
Organizations must protect employee data from the early stages by aligning recruitment workflows with data privacy laws. Following data protection regulation gdpr principles ensures lawful handling, while a data protection impact assessment helps reduce risks around employee data privacy and private data exposure.
Pre-Employment Verification Data
Once an offer is made, organizations collect employee data, including right-to-work documents, tax identification numbers, banking details for direct deposit, and background check results. Right-to-work verification documents like passports contain highly sensitive personal data that attracts identity theft attempts. Secure storage and encryption during the transfer of data between systems becomes critical at this stage, especially when using centralized recruitment management software to automate hiring workflows.
Teams must protect employee data by applying strict data privacy laws and following data protection regulation gdpr. Conducting a data protection impact assessment ensures risks are addressed. Encrypt data when transferring sensitive employee data to prevent private data leaks and strengthen employee data privacy.
Onboarding Documentation And Personal Records
Onboarding expands data collection to emergency contacts, insurance beneficiary information, tax withholding forms, and benefits enrollment. Health and benefits data enters here and requires separation from general HR files. Data minimization applies even during onboarding. If a health plan does not require collecting specific medical history, avoid gathering it unnecessarily.
Organizations should protect employee data by limiting unnecessary collection under data privacy laws. Data protection regulation gdpr requires lawful processing, while a data protection impact assessment identifies exposure risks. Encrypt data during storage to safeguard private data and maintain strong employee data privacy practices.
Employee Lifecycle Data Generation
Once employed, data accumulates continuously through payroll records, performance reviews, sickness records, benefits utilization, training records, and disciplinary actions. Processing personal data during daily operations requires clear role-based access so payroll specialists see financial data while line managers access only their team’s performance information, supported by robust employee role management software for HR and payroll.
To protect employee data, organizations must align operations with data privacy laws and data protection regulation gdpr. Conduct a data protection impact assessment regularly. Encrypt data across systems to secure private data and ensure employee data privacy throughout continuous data processing activities.
Exit And Offboarding Data Handling
HR responsibilities extend beyond an employee’s last working day. Tax records must be retained for typically six years. Litigation holds might require retaining email and documents related to the former employee's data. Secure deprovisioning requires revoking all system access, migrating document ownership, and logging all access changes immediately upon departure.
Organizations must protect employee data even after exit by following data privacy laws and data protection regulation gdpr. A data protection impact assessment ensures risks remain controlled. Encrypt data archives to secure private data and maintain employee data privacy for former employees.
How To Map HR Data Across The Employee Lifecycle
Data mapping is the foundational practice that enables effective hr data protection. Before implementing security controls or compliance measures, HR teams must know what data they hold, where it lives, how long they keep it, who touches it, and the lawful basis for retention.
Main categories include identification data like names and national IDs, employment data including contracts and performance records, financial data such as bank accounts and tax codes, health and benefits information, and system logs capturing activity data, all of which benefit from a centralized employee record management system for modern HR teams. Data flows between ATS, HRIS, payroll, time tracking, and collaboration platforms. Each integration point represents potential exposure where data might be duplicated or retained unexpectedly, making secure and well-planned HR data migration processes critical when systems change.
Recruitment And Pre Employment Stage
HR should minimize data at recruitment by avoiding the collection of national ID numbers until an offer is accepted. Disclosure requirements in many regions mean candidates must understand why their information is collected and how long it remains in talent pools. The typical retention period for unsuccessful candidates is six to twelve months unless they provide employee consent for longer retention.
Employment and Day-to-Day HR Operations
Data sensitivity grows during employment. Role-based access ensures payroll staff see banking details while managers see performance reviews for their direct reports only. Lawful monitoring of VPN access, time tracking, and device logs requires clear policies and appropriate notice to employees about inform employees regarding monitoring scope.
Offboarding, Retention, And Post Employment
Concrete retention examples vary by geography. UK tax records typically require six years. FCRA employment records need three years. Organizations should document retention rules in writing and implement system-based deletion rather than relying on manual processes. Anonymization and pseudonymization allow keeping historical data for benchmarking without storing employee data with personal identifiers, while well-governed employee payroll records management ensures retained data remains accurate and compliant.
Best Security Practices For HR Data Protection
Data encryption at rest protects stored information while encryption in transit secures data moving between systems. Encrypted payslip delivery through secure portals rather than email attachments reduces exposure. Endpoint security for HR staff includes full disk encryption, screen locks, and remote wipe capability for lost devices.
Regular security audits and vendor assessments help identify vulnerabilities. Reputable HR vendors should have SOC 2 Type II or ISO 27001 certification demonstrating independent verification of security controls and data compliance practices, alongside mature HR role permission systems for secure access control.
Access Management And Least Privilege In HR
The principle of least privilege means employees have access only information necessary for their specific role. HR assistants might see directory information but not salary data. Payroll specialists see financial records but not disciplinary files. Line managers see their team’s performance data but not that of other departments. Strict access controls prevent permission sprawl that increases breach risk.
Timely access revocation at role changes and departures requires attention. Logging and access logs for sensitive actions support both security and trust when disputes arise about who accessed what data, and centralized HR dashboard software with real-time visibility can surface these access trends to leadership.
Incident Response For HR Data Breaches
Data breaches in HR take many forms, including misdirected payslips, lost devices, compromised credentials, and ex-employee access that was never revoked. A simple incident response flow includes detect, contain, assess, notify, and learn phases, with HR’s specific role at each step.
GDPR requires breach notifications to regulators within 72 hours where high risk exists to individuals. Notification to affected employees may also be required. Documenting incident response decisions protects organizations if regulators later inquire about handling.
Governance, Policies, And HR Culture Around Data Protection
Data protection governance means assigning clear accountability, defining policies, and creating mechanisms that make protecting data everyone’s responsibility.
Define Clear HR Data Handling Policies
Policies translate regulatory requirements into operational guidance. An HR data handling policy should specify what data the organization collects at each lifecycle stage and why, how long data is retained with specific timelines by category and jurisdiction, who can access what data under what circumstances, and what happens if violations occur. Policies should be specific enough to guide behavior but written in language HR employees understand without legal degrees.
Train Teams On Data Security Best Practices
Employee training ensures HR professionals understand their responsibilities for hr data security and know how to handle sensitive information appropriately. Training should cover role specific responsibilities, recognizing phishing attempts, password security practices, and proper use of shared systems when working remotely. Training timing matters with onboarding sessions for new HR employees and annual refreshers for the whole team.
Assign Roles And Accountability For Data Protection
Clear ownership requires defining who is responsible for what. A data protection officer oversees compliance and manages data subject requests. HR leadership ensures teams follow policies. IT leadership manages technical controls including robust security measures. Line managers ensure their teams follow handling policies. Each person should understand their role, authority, and accountability for processing data appropriately.
Encourage Secure Communication Across Departments
HR data privacy requires coordination across IT, legal, finance, and business units. Creating mechanisms for secure communication includes establishing a data protection committee that meets regularly, defining escalation paths when employees discover potential breaches, and establishing cross functional data sharing agreements. When legal needs employee data for litigation, secure export through encrypted portals with audit trails limits exposure.
Monitor Behavior And Reinforce Security Standards
Ongoing monitoring reinforces standards established through policies and training. Access reviews quarterly confirm appropriate permissions. Audit log reviews identify unusual patterns like data access at unusual times or bulk downloads. Incident trending reveals whether recurring issues indicate process problems. When violations occur, proportionate responses from educational correction to progressive discipline maintain accountability.
How To Build A Culture Of Data Protection Awareness
Building culture where data protection is a shared value requires leadership commitment, clear messaging, and recognition that protecting employee information is core to how the organization operates, especially as HR automation trends in 2026 reshape how data flows through HR systems.
Define Clear HR Data Handling Policies
HR departments should document specific procedures for each data type and lifecycle stage. Policy documents should specify retention periods by jurisdiction, identify who needs access to what information, and establish clear consequences for policy violations. Regular policy reviews ensure guidance stays current with evolving data privacy regulations and organizational changes.
Train Teams On Data Security Best Practices
Practical training uses real scenarios rather than abstract compliance lectures. Show HR teams how to respond when an ex-employee emails requesting their employment records. Demonstrate secure document sharing alternatives to personal email. Cover recognizing phishing attempts and proper use of limit access controls. Measure training effectiveness through behavior change metrics rather than just completion rates.
Assign Roles And Accountability For Data Protection
Authority must accompany accountability. The data protection officer should have direct access to senior leadership to report on data protection status. HR leadership should have the authority to reject vendor contracts that fail to meet security standards. Relevant stakeholders throughout the organization should understand their specific responsibilities for protecting sensitive employee data.
Encourage Secure Communication Across Departments
Cross-functional collaboration protects consumer data and employee information simultaneously. When IT discovers a potential vulnerability affecting HR systems, clear communication channels ensure rapid response, particularly in distributed teams using cloud HR tools for remote team management. When HR needs to share employee records with external auditors, defined procedures specify secure transfer methods. Regular communication about data protection status keeps the topic visible across the organization.
Monitor Behavior And Reinforce Security Standards
Continuous monitoring supports compliance without creating a surveillance culture. Quarterly access reviews verify appropriate permissions. Automated alerts flag unusual access patterns for investigation. Risk management processes identify emerging threats before they cause breaches. Celebrating employees who identify and report security concerns reinforces positive behaviors.
Update Practices Based On Emerging Security Risks
Security threats evolve continuously. Organizations should maintain awareness through regulatory guidance updates, industry bulletins covering HR specific threats, and vendor security notifications, especially when relying on HR platforms to manage a remote workforce effectively. As AI tools become more common in recruitment and performance management, evaluating vendor security controls and legal compliance for these new tools becomes essential for data privacy compliance.
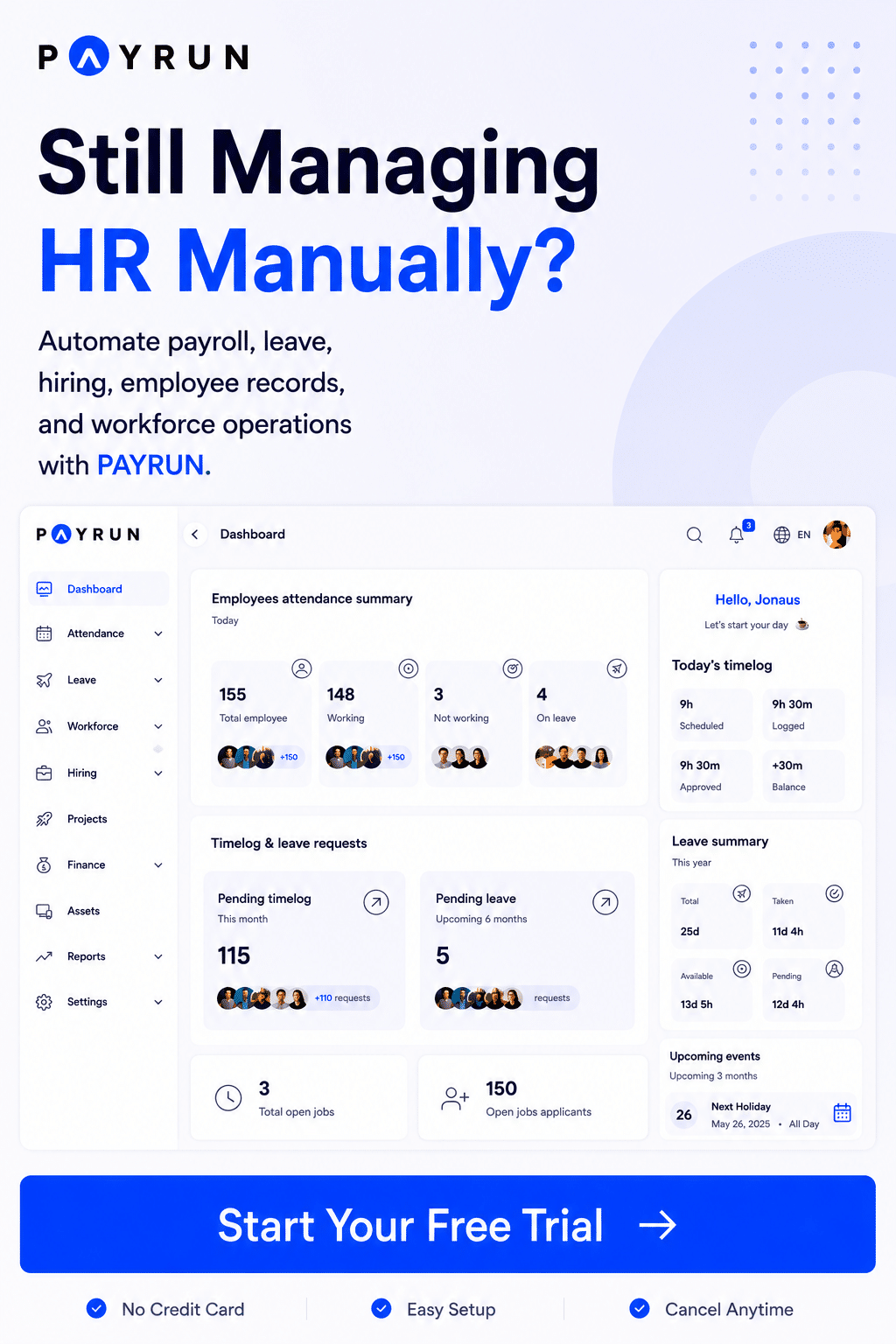
How Payrun Supports HR Data Protection Across The Employee Lifecycle
Payrun centralizes payroll and key HR data in one secure environment, reducing the spread of sensitive personal information across spreadsheets and ad hoc tools. The platform provides granular role based access controls so organizations can configure exactly what each role views, edits, or exports, delivering all-in-one HR platform simplicity for data protection.
Technical safeguards include data encryption at rest and in transit, detailed activity logs on payroll and user actions, and secure payslip delivery through encrypted portals. Workflows support lifecycle specific needs from new starter setup through leaver processing with consistent access rules and audit trails throughout.
For organizations storing employee data across multiple jurisdictions, Payrun’s configuration options help align with retention policies and legal obligation requirements. The platform handles PAYE and statutory contributions accurately while maintaining clear records that support audits. Explore Payrun's innovative HR features to strengthen your approach to hr data management through a demo or trial.
Frequently Asked Questions
How Long Should We Keep Employee Records After Someone Leaves?
Retention varies by jurisdiction and record type. UK tax records typically require six years, while FCRA employment records need three years. Health records under HIPAA often require three to six years. Document your retention rules in a schedule and apply them consistently. System-based retention automates deletion rather than relying on manual processes that may be forgotten.
Do We Always Need Consent To Process Employee Data?
No. Under GDPR and similar laws, HR often relies on contract, legal obligation, or legitimate interests rather than consent for core employment data. Consent remains useful for optional activities like wellness programs or marketing photos. When consent is required, it must be freely given, specific, informed, and easy to withdraw. Gain employee consent only when truly necessary.
How Can Small HR Teams Improve Data Protection Without A Big Budget?
Start with fundamentals. Centralize data into secure HR software for small and medium businesses rather than spreadsheets. Enforce strong passwords and multi-factor authentication. Run short internal training sessions. Use built-in security features of existing tools, including access roles and audit logs, and, where possible, replace disconnected HR tools with a unified platform to reduce risk. Choosing HR software tailored for small businesses can offload technical security controls from small teams.
What Should We Do If An Employee Asks For A Copy Of All Their Data?
This constitutes a data subject access request with formal timelines under laws like GDPR. Verify identity, gather data from HR and payroll systems, remove information about other people, and respond within required timeframes. Setting up repeatable processes using system exports avoids last-minute manual searches when requests arrive.
Is It Safe To Use AI Tools With Employee Information?
Many generic AI tools create serious data privacy and confidentiality risks when used with biometric data or other sensitive information. Establish clear internal rules prohibiting pasting CVs, salary data, or health information into public AI services. Where AI features exist within HR systems, verify vendors have proper data processing agreements and collect data only as needed for specific purposes.